When it comes to catching cheating students in Higher Education, there’s a lot of noise. It’s easy to be fooled by the latest in greatest “technology”, but ultimately success boils down to a few key ingredients!
It all starts with effective, continuous student ID authentication (not to mention it’s a federal mandate).
We’re not talking about the flash of a driver’s license through a webcam right before an exam. OR face detection, that only checks if there’s a human present. Note, this should not be confused with face recognition which is when you compare one face’s geometry to the same or different face. Many proctoring companies use face detection so do not be fooled thinking they are determining if it’s the same student – they do not know who it is! There is no template to compare to. This by the way is the first rule of biometrics, make sure your vendor can prove they are taking a template. Or this will happen: https://www.vice.com/en/article/g5gxg3/proctorio-is-using-racist-algorithms-to-detect-faces.
True identity authentication requires a solution that’s used early/often and that’s compared against a previously created template. Enter BioSig-ID™; a patented gesture biometric proven effective after millions of ID authentications that takes only seconds to use.
Best of all. BioSig-ID does not require any special hardware or software downloads. It can be reset like a regular password and you do not have to worry about privacy violations or any concerns regarding racial bias-both worrisome when using facial biometrics.
Methodology and key learning:
- Our data indicates cheating happens at every opportunity throughout a course: tests, paper submissions, quizzes, discussion threads, in fact, any assessments that count for a grade.
- Continuous ID authentication in multiple assessments using true authentication with a biometric throughout the course is crucial to look for cheating patterns
- Schools tend to focus on a midterm or final exams for cheating. In the past, you could not “proctor” assessments other than an exam. This allows free access to cheating in all other areas of the course. They do not provide a barrier beyond password access which means anyone can do the work if they know the password
- Our data suggests that over 50% of cheating occurs on any project that counts towards a grade. Since BioSig-ID authentication takes only seconds to complete and performs ID authentication immediately using conditional release, clients add authentication challenges to those areas. Otherwise, the “barn door” is way open to enable cheating. Clients can also add a timed challenge, requiring students to authenticate their ID every 30 minutes or set up random challenges
- Without ID authentication, anybody can use the student’s password, complete the assessment and NOBODY at the school is the wiser. BioSig-ID is the first to provide true identity authentication as a barrier within the LMS. Thanks to our patented technology, paid “helpers” have to reproduce the same unique drawn password which is nearly impossible even if they know what the password is. If the student is unable to successfully authenticate their identity, we presume it is not the registered student and access is denied. “No access, no cheating”
- Pattern history should include minimally, operating system and browser use, password resets, physical location, time, activity, application, level of success, accuracy of passwords, history, stroke count, type of activity, IP location, VPN use and more.
- Students or paid “helpers” leave a trail that makes it extremely easy to establish patterns of cheating. With history, repeated behaviors are identified as we force rank to identify the most suspicious patterns
- When pattern irregularities occur, we immediately issue real-time event notifications (RTENS) to clients indicating a problem. We then provide detailed reports of the activity. For example, a student using a new device, starting a new course, different IP location all happening at the same time creates a yellow flag
- An example of pattern irregularities would be if the student uses a password reset and starts a new course from a new IP. This creates an RTEN sent to the client and BSI forensics experts who then focus in on the total student patterns looking for more evidence of cheating behaviors
- Higher-level risk assessments rely on a convergence of movements coming from the device used and a trust assessment is then based on historical patterns to identify atypical new patterns and scores.
- The output of these adaptive searches is realized in 30 + easy-to-read reports. The end result is a ranking of highest to lowest risk users
- Using our AI, student’s password patterns are assessed and a score created based on accuracy, stroke count and other parameters compared to their history. For example, if a student regularly completed his or her password in 10 seconds but is now taking 30-40 seconds with multiple attempts, this is flagged and our experts decide whether or not to investigate
- BSI also uses some proprietary techniques to assess identity and risk factors that prevent us from sharing in this forum.
Summary:
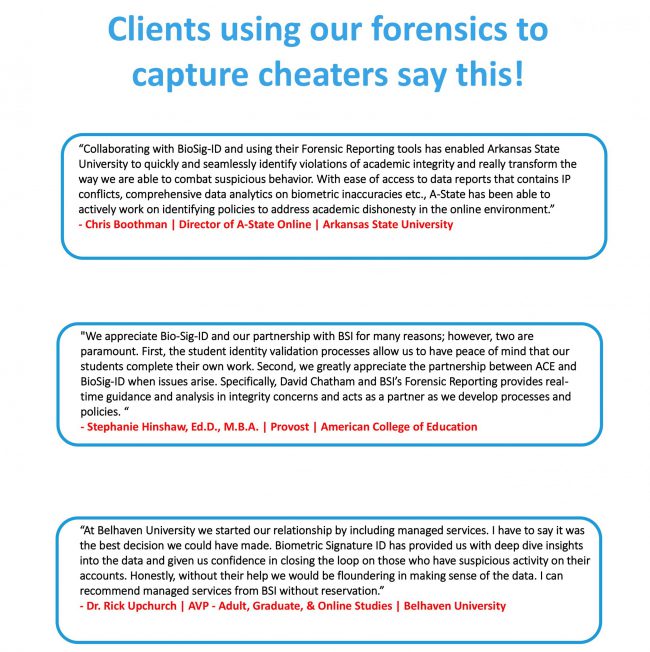
It is uncommon for an institution to use data analytics and algorithms to identify cheating patterns and other historical data. This is why our clients use BSI expertise regularly as a valuable outsourced service for business-critical data. As part of BSI’s service, we also compare your students to other like schools, suggest new policies, offer new tips on determining the next steps after a cheating student is identified, and how to prevent further cheating in your school.
BSI has identified 1,000’s of students who have made poor integrity judgments. We provide you with the granular data needed to enable you to immediately move into action without spending time chasing data.
Give us a call to see actual examples of cheating students and discover how we can help you detect and prevent the cheating you already know exists, but are powerless to stop.
Sales: Tyler Weiland | 972–571–7834 | Tyler.Weiland@biosig- id.com